11 public key configuration, Asymmetric key algorithm overview, Basic concepts – H3C Technologies H3C S7500E Series Switches User Manual
Page 196: Key algorithm types, Public key configuration
11-1
11
Public Key Configuration
This chapter includes these sections:
z
Asymmetric Key Algorithm Overview
z
Configuring the Local Asymmetric Key Pair
z
Configuring the Public Key of a Peer
z
Displaying and Maintaining Public Keys
z
Public Key Configuration Examples
Asymmetric Key Algorithm Overview
Basic Concepts
z
Algorithm: A set of transformation rules for encryption and decryption.
z
Plain text: Information without being encrypted.
z
Cipher text: Encrypted information.
z
Key: A string of characters that controls the transformation between plain text and cipher
text. It participates in both the encryption and decryption.
Key Algorithm Types
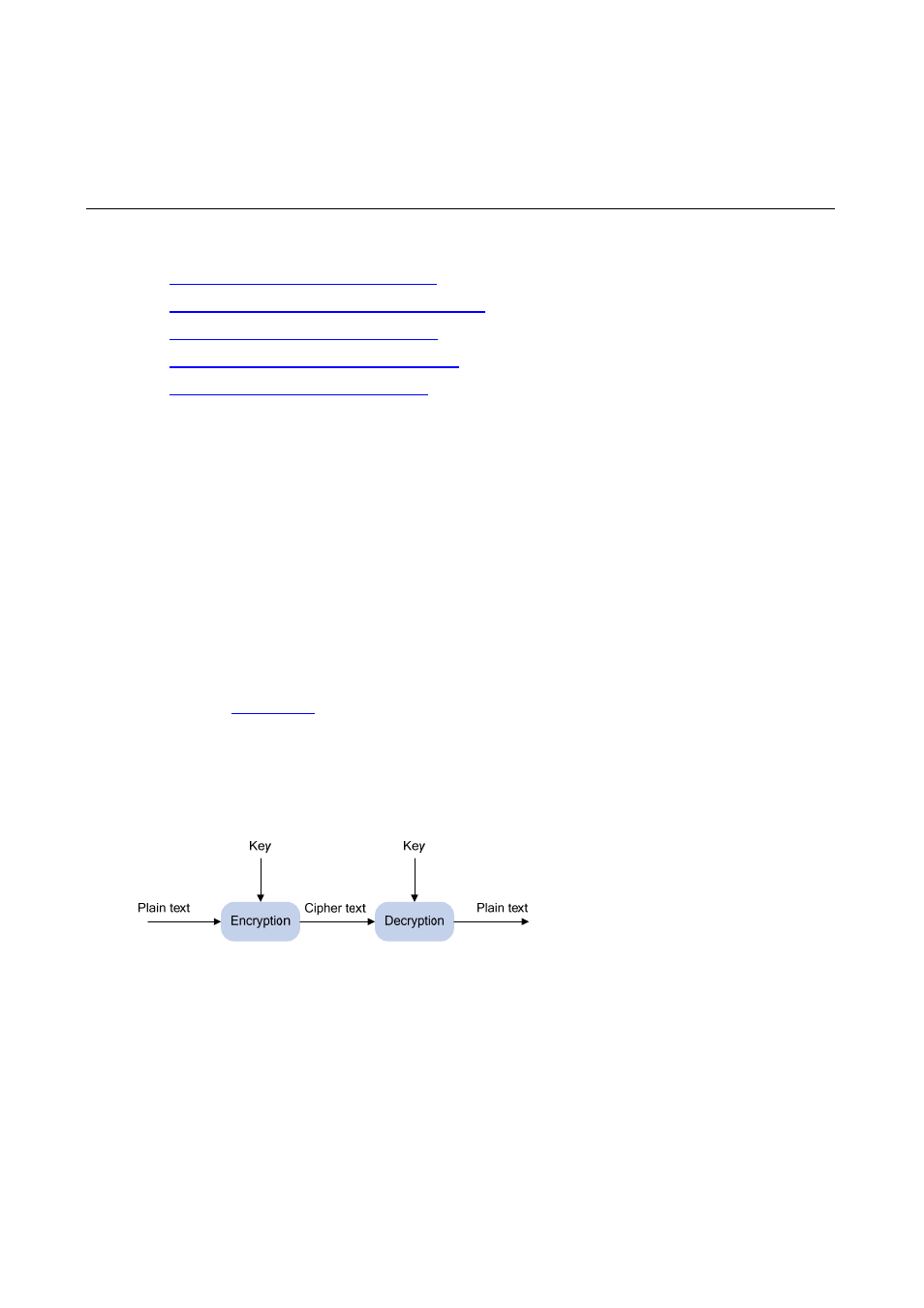
As shown in
, the information in plain text is encrypted by an algorithm with the help
of a key before being sent. The resulting cipher text is transmitted across the network to the
receiver, where it is decrypted by the same algorithm also with the help of a key to obtain the
original plain text.
Figure 11-1 Encryption and decryption
There are two types of key algorithms, based on whether the keys for encryption and decryption
are the same:
z
Symmetric key algorithm: The keys for encryption and decryption are the same. Commonly
used symmetric key algorithms include Advanced Encryption Standard (AES) and Data
Encryption Standard (DES).
z
Asymmetric key algorithm: The keys for encryption and decryption are different, one is the
public key, and the other is the private key. The information encrypted with the public key
can only be decrypted with the corresponding private key, and vice versa. The private key