Configuring an acl – H3C Technologies H3C S12500-X Series Switches User Manual
Page 145
133
3.
Configure an IPsec policy to associate data flows with the IPsec transform sets, specify the SA
negotiation mode, the peer IP addresses (the start and end points of the IPsec tunnel), the required
keys, and the SA lifetime.
An IPsec policy is a set of IPsec policy entries that have the same name but different sequence
numbers. In the same IPsec policy, an IPsec policy entry with a smaller sequence number has a
higher priority.
4.
Apply the IPsec policy to an interface.
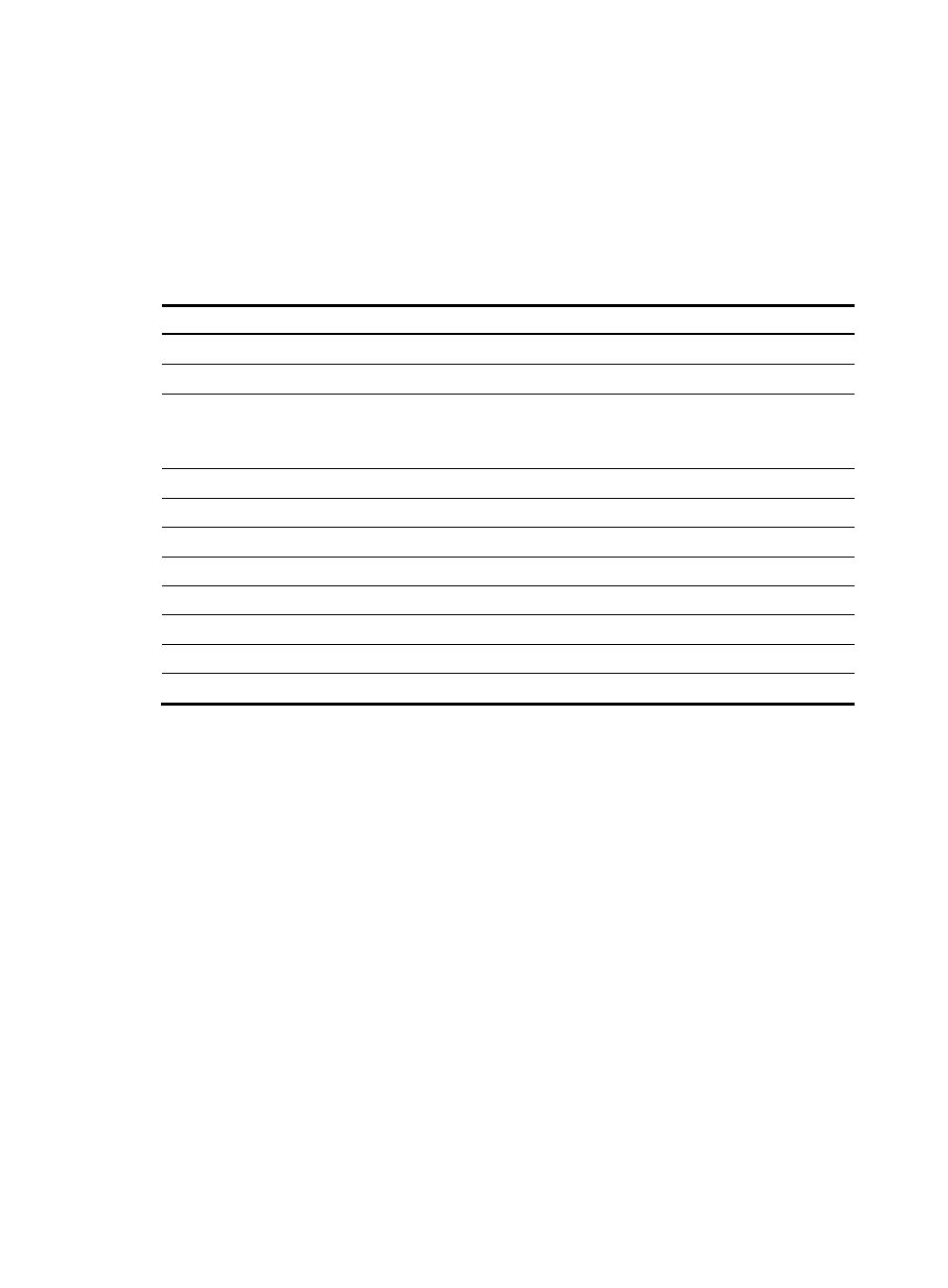
Complete the following tasks to configure ACL-based IPsec:
Tasks at a glance
(Required.)
842H
Configuring an ACL
(Required.)
843H
Configuring an IPsec transform set
(Required.) Configure an IPsec policy (use either method):
•
844H
Configuring a manual IPsec policy
•
845H
Configuring an IKE-based IPsec policy
(Required.)
846H
Applying an IPsec policy to an interface
(Optional.)
847H
Enabling ACL checking for de-encapsulated packets
(Optional.)
848H
Configuring the IPsec anti-replay function
(Optional.)
849H
Binding a source interface to an IPsec policy
(Optional.)
850H
Enabling QoS pre-classify
(Optional.)
851H
Enabling logging of IPsec packets
(Optional.)
852H
Configuring the DF bit of IPsec packets
(Optional.)
853H
Configuring SNMP notifications for IPsec
238B
Configuring an ACL
IPsec uses ACLs to identify the traffic to be protected.
466B
Keywords in ACL rules
An ACL is a collection of ACL rules. Each ACL rule is a deny or permit statement. A permit statement
identifies a data flow protected by IPsec, and a deny statement identifies a data flow that is not protected
by IPsec. With IPsec, a packet is matched against the referenced ACL rules and processed according to
the first rule that it matches:
•
Each ACL rule matches both the outbound traffic and the returned inbound traffic.
•
In the outbound direction, if a permit statement is matched, IPsec considers that the packet requires
protection and continues to process it. If a deny statement is matched or no match is found, IPsec
considers that the packet does not require protection and delivers it to the next function module.
•
In the inbound direction:
{
Non-IPsec packets that match a permit statement are dropped.
{
IPsec packets that match a permit statement and are destined for the device itself are
de-encapsulated. By default, the device matches the de-encapsulated packets against the ACL
again and, if they match a permit statement, continues to process the packets. If ACL checking
- H3C S5560 Series Switches H3C WX6000 Series Access Controllers H3C WX5000 Series Access Controllers H3C WX3000 Series Unified Switches H3C LSWM1WCM10 Access Controller Module H3C LSWM1WCM20 Access Controller Module H3C LSQM1WCMB0 Access Controller Module H3C LSRM1WCM2A1 Access Controller Module H3C LSBM1WCM2A0 Access Controller Module H3C S9800 Series Switches H3C S5130 Series Switches H3C S5120 Series Switches