Secure keys generation – Rose Electronics UltraMatrix Remote 2 User Manual
Page 21
ULTRAMATRIX REMOTE 2 INSTALLATION AND OPERATIONS MANUAL
15
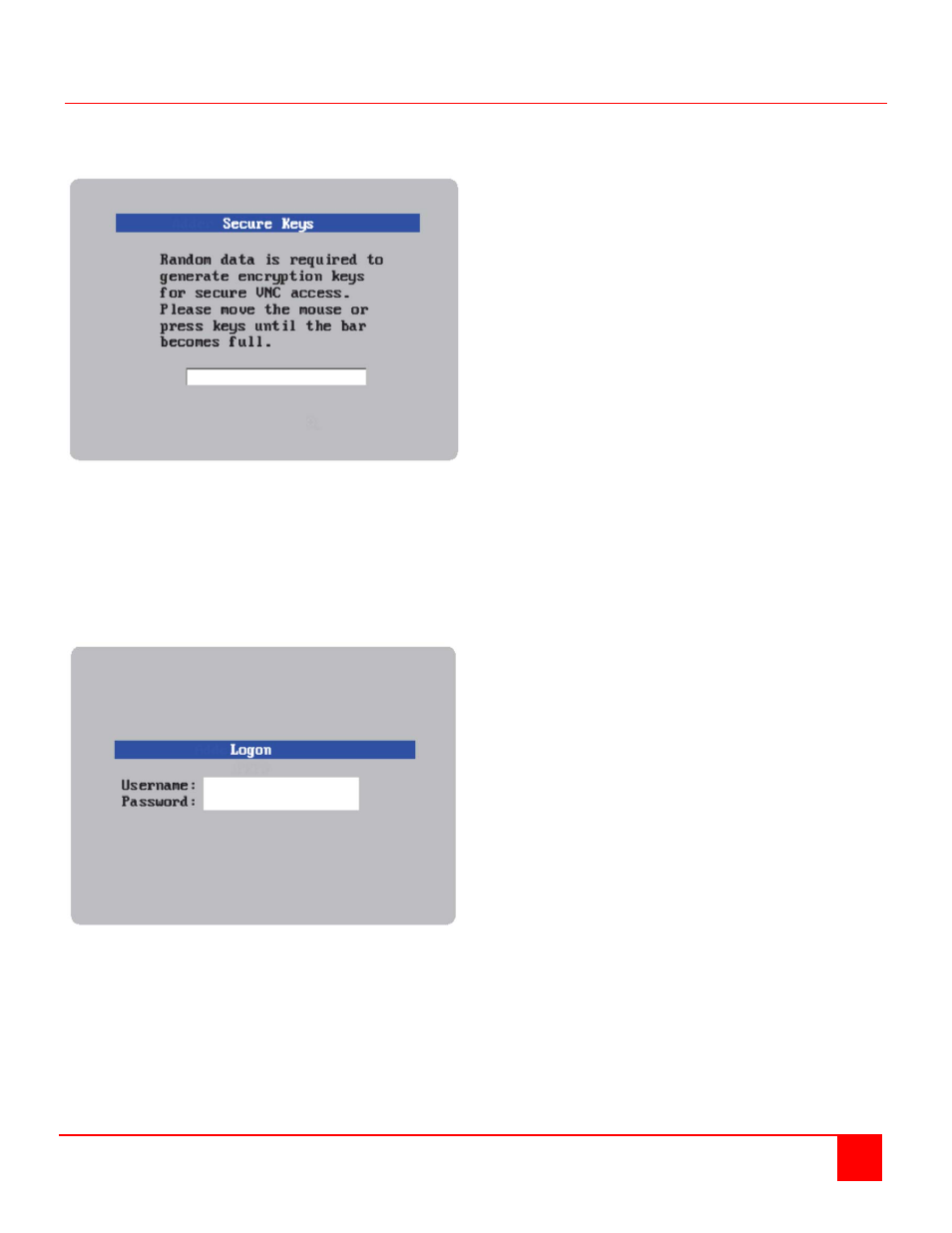
Secure Keys Generation
The Secure keys screen uses mouse movements and keyboard inputs to create random data. This unpredictable
information is then combined with several other factors to develop the basis of the encryption keys that are used to
establish secure remote links.
Figure 12. Secure Keys
With every mouse move and key press the single dash will move across the progression bar (unless the same key is
pressed repeatedly). Periodically, a new star character will be added to the bar as the random data are accepted as
part of the new encryption key. When the bar is full, the final encryption keys for your UltraMatrix Remote 2 will be
created – this process takes roughly 30 to 40 seconds.
Once the secure key has been calculated, the UltraMatrix Remote 2 will restart and present a standard logon screen
as shown below.
Figure 13. Logon Screen
Logon using “admin” as the Username and the password that was entered on the Unit Configuration setup screen.
Upon validation, the KVM monitor screen will show the host computers video.
Repeat this configuration process for each IP input module by connecting to the next KVM input port.