Configuration prerequisites, Configuration procedure, Ignoring authorization information from the server – H3C Technologies H3C S12500-X Series Switches User Manual
Page 142: Security association, Authentication and encryption
130
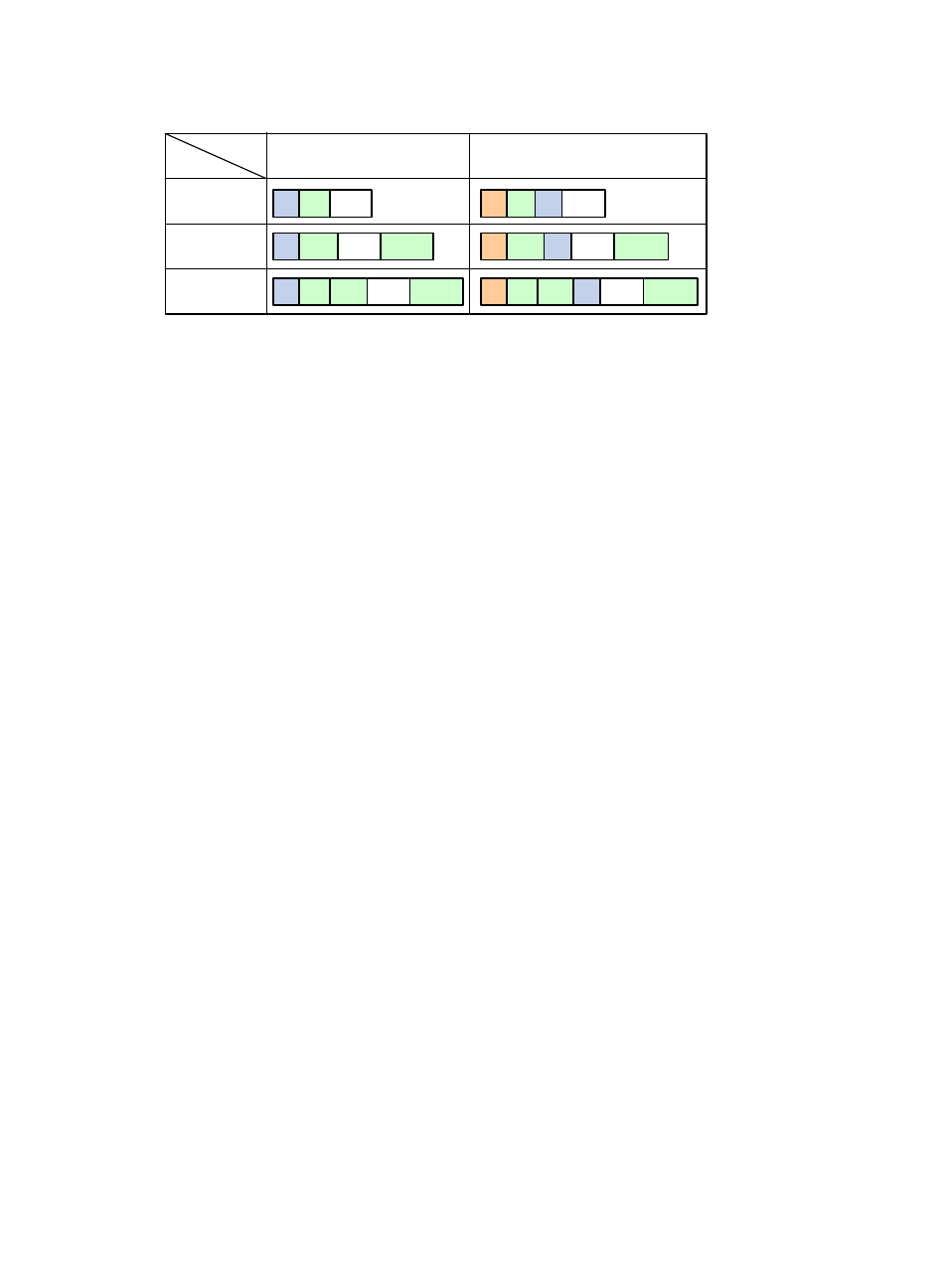
Figure 42 Security protocol encapsulations in different modes
232B
Security association
A security association (SA) is an agreement negotiated between two communicating parties called
"IPsec peers." An SA comprises a set of parameters for data protection, including security protocols (AH,
ESP, or both), encapsulation mode (transport mode or tunnel mode), authentication algorithm
(HMAC-MD5 or HMAC-SHA1), encryption algorithm (DES, 3DES, or AES), and shared keys and their
lifetimes.
An SA is unidirectional. At least two SAs are needed to protect data flows in a bidirectional
communication. If two peers want to use both AH and ESP to protect data flows between them, they
construct an independent SA for each protocol in each direction.
An SA is uniquely identified by a triplet, which consists of the security parameter index (SPI), destination
IP address, and security protocol identifier. An SPI is a 32-bit number that identifies an SA. It is transmitted
in the AH/ESP header.
An SA can be set up manually or through IKE.
•
Manual mode—Configure all parameters for the SA through commands. This configuration mode
is complex and does not support some advanced features (such as periodic key update), but it can
implement IPsec without IKE. This mode is mainly used in small and static networks or when the
number of IPsec peers in the network is small.
•
IKE negotiation mode—The peers negotiate and maintain the SA through IKE. This configuration
mode is simple and has good expansibility. In medium- and large-scale dynamic networks, H3C
recommends setting up SAs through IKE negotiations.
A manually configured SA never ages out. An IKE-created SA has a lifetime, which comes in two types:
•
Time-based lifetime—Defines how long the SA can be valid after it is created.
•
Traffic-based lifetime—Defines the maximum traffic that the SA can process.
If both lifetime timers are configured for an SA, the SA becomes invalid when either of the lifetime timers
expires. Before the SA expires, IKE negotiates a new SA, which takes over immediately after its creation.
233B
Authentication and encryption
462B
Authentication algorithms
IPsec uses hash algorithms to perform authentication. A hash algorithm produces a fixed-length digest for
an arbitrary-length message. IPsec peers respectively calculate message digests for each packet. The
receiver compares the local digest with that received from the sender. If the digests are identical, the
receiver considers the packet intact and the sender's identity valid. IPsec uses the Hash-based Message
Mode
Protocol
Transport
Tunnel
AH
ESP
AH-ESP
ESP-T
IP
Data
ESP
AH
IP
ESP-T
IP
Data
ESP
IP
IP
Data
AH IP
IP
Data
AH
ESP-T
IP
Data
ESP
ESP-T
IP
Data
ESP
AH