Displaying and maintaining ike, Configuration procedure, Configuration example – H3C Technologies H3C S12500-X Series Switches User Manual
Page 232
220
304B
Configuration procedure
To configure source MAC-based ARP attack detection:
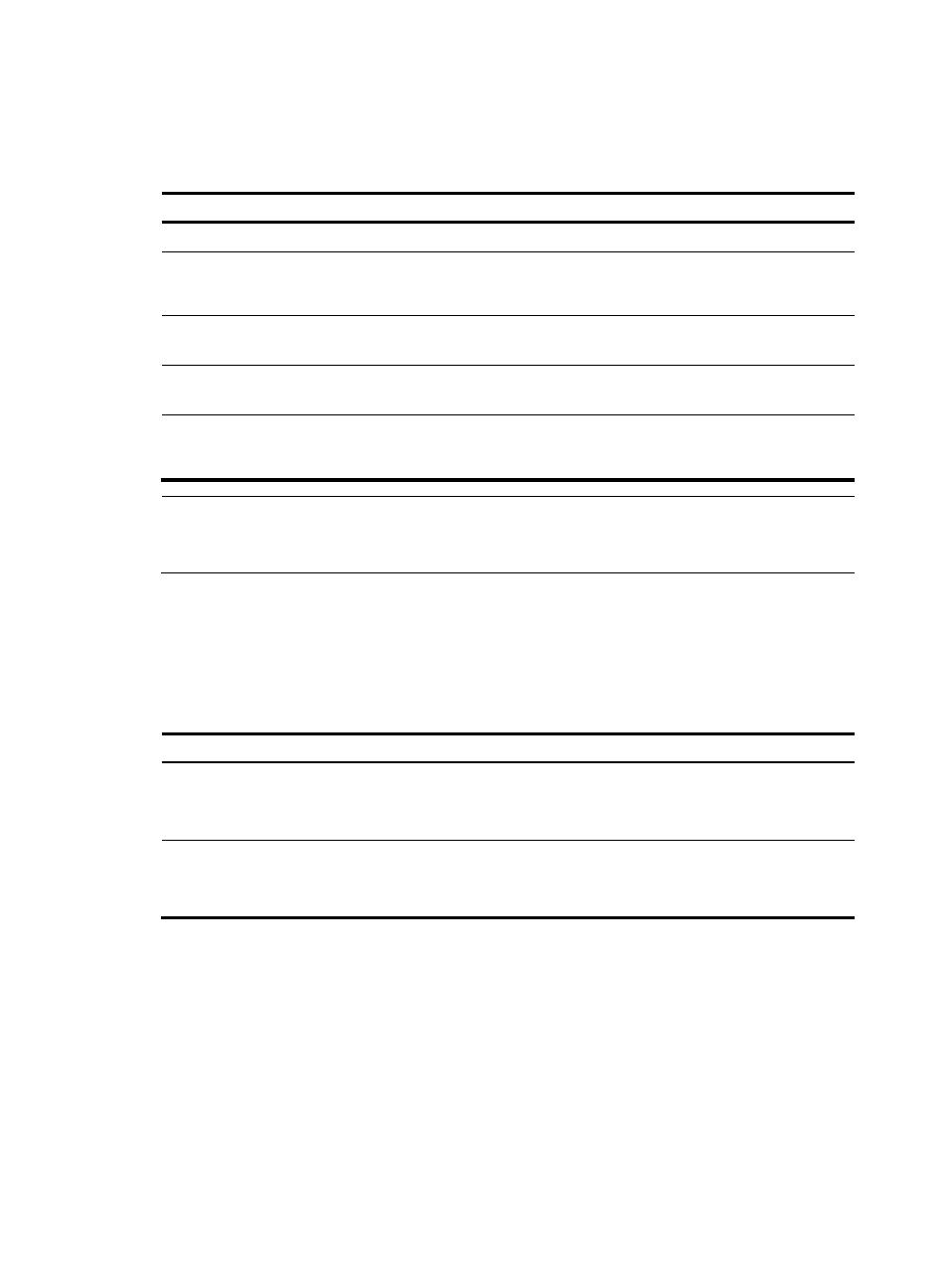
Step Command
Remarks
1.
Enter system view.
system-view
N/A
2.
Enable source MAC-based
ARP attack detection and
specify the handling method.
arp source-mac { filter | monitor }
By default, this feature is disabled.
3.
Configure the threshold.
arp source-mac threshold
threshold-value
The default threshold is 30
packets.
4.
Configure the aging timer for
ARP attack entries.
arp source-mac aging-time time
By default, the lifetime is 300
seconds.
5.
(Optional.) Exclude specified
MAC addresses from this
detection.
arp source-mac exclude-mac
mac-address&<1-10>
By default, no MAC address is
excluded.
NOTE:
When an ARP attack entry expires, ARP packets sourced from the MAC address in the entry can be
processed correctly.
305B
Displaying and maintaining source MAC-based ARP attack
detection
Execute display commands in any view.
Task Command
Display ARP attack entries detected by source
MAC-based ARP attack detection (in standalone
mode).
display arp source-mac { slot slot-number | interface
interface-type interface-number }
Display ARP attack entries detected by source
MAC-based ARP attack detection (in IRF mode).
display arp source-mac { chassis chassis-number slot
slot-number | interface interface-type interface-number }
306B
Configuration example
529B
Network requirements
As shown in
931H
Figure 69
, the hosts access the Internet through a gateway (Device). If malicious users send
a large number of ARP requests to the gateway, the gateway might crash and cannot process requests
from the clients. To solve this problem, configure source MAC-based ARP attack detection on the
gateway.