Configuring a bsr, Configuring a c-bsr – H3C Technologies H3C S12500 Series Switches User Manual
Page 148
132
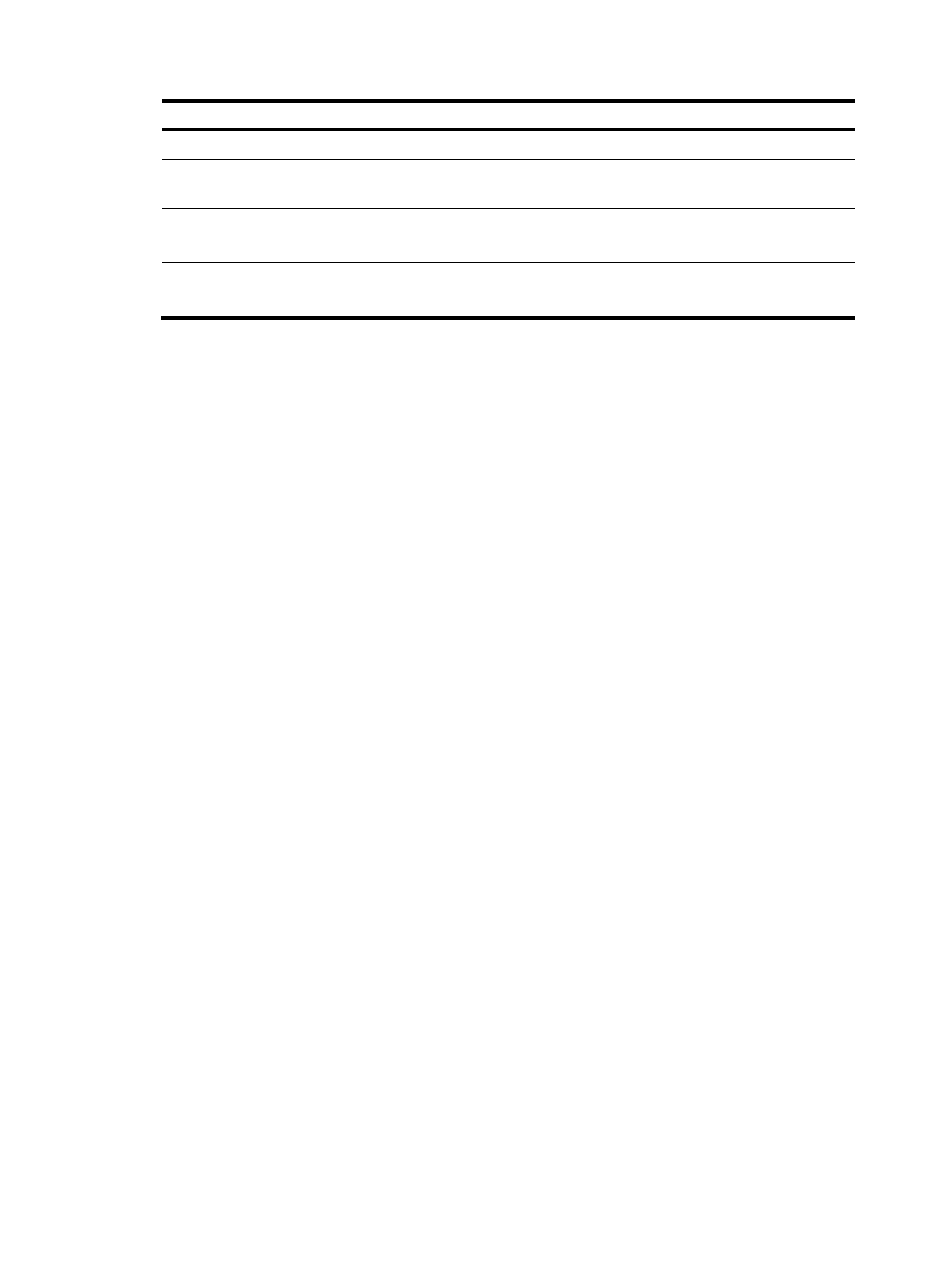
Step
Command
Remarks
1.
Enter system view.
system-view
N/A
2.
Enter public network PIM view
or VPN instance PIM view.
pim [ vpn-instance
vpn-instance-name ]
N/A
3.
Configure the C-RP-Adv
interval.
c-rp advertisement-interval interval
Optional.
60 seconds by default.
4.
Configure C-RP timeout time.
c-rp holdtime interval
Optional.
150 seconds by default.
For more information about the configuration of other timers in PIM-SM, see "
Configuring a BSR
A PIM-SM domain can have only one BSR, but must have at least one C-BSR. Any router can be
configured as a C-BSR. Elected from C-BSRs, the BSR is responsible for collecting and advertising RP
information in the PIM-SM domain.
Configuring a C-BSR
C-BSRs should be configured on routers in the backbone network. When you configure a router as a
C-BSR, be sure to specify a PIM-SM-enabled interface on the router. The BSR election process is
summarized as follows:
1.
Initially, every C-BSR assumes itself to be the BSR of this PIM-SM domain, and uses its interface IP
address as the BSR address to send bootstrap messages.
2.
When a C-BSR receives the bootstrap message of another C-BSR, it first compares its own priority
with the other C-BSR's priority carried in message. The C-BSR with a higher priority wins. If a tie
exists in the priority, the C-BSR with a higher IP address wins. The loser uses the winner's BSR
address to replace its own BSR address and no longer assumes itself to be the BSR, and the winner
retains its own BSR address and continues assuming itself to be the BSR.
Configuring a legal range of BSR addresses enables filtering of bootstrap messages based on the
address range, thus to prevent a maliciously configured host from masquerading as a BSR. The same
configuration must be made on all routers in the PIM-SM domain. The following are typical BSR spoofing
cases and the corresponding preventive measures:
•
Some maliciously configured hosts can forge bootstrap messages to fool routers and change RP
mappings. Such attacks often occur on border routers. Because a BSR is inside the network whereas
hosts are outside the network, you can protect a BSR against attacks from external hosts by enabling
the border routers to perform neighbor checks and RPF checks on bootstrap messages and discard
unwanted messages.
•
When an attacker controls a router in the network or when an illegal router is present in the network,
the attacker can configure this router as a C-BSR and make it win BSR election to control the right
of advertising RP information in the network. After a router is configured as a C-BSR, it automatically
floods the network with bootstrap messages. Because a bootstrap message has a TTL value of 1, the
whole network will not be affected as long as the neighbor router discards these bootstrap
messages. Therefore, with a legal BSR address range configured on all routers in the entire network,
all these routers will discard bootstrap messages that are not in the legal address range.