Use of the permit/deny actions in acls – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 871
850
Use of the Permit/Deny Actions in ACLs
IPsec uses ACLs to identify data flows. An ACL is a collection of ACL rules. Each ACL rule is a deny or
permit statement. A permit statement identifies a data flow protected by IPsec, and a deny statement
identifies a data flow that is not protected by IPsec. IPsec uses referenced ACL to match against packets.
The matching process stops once a match is found or ends with no match hit. The packet is handled as
follows:
•
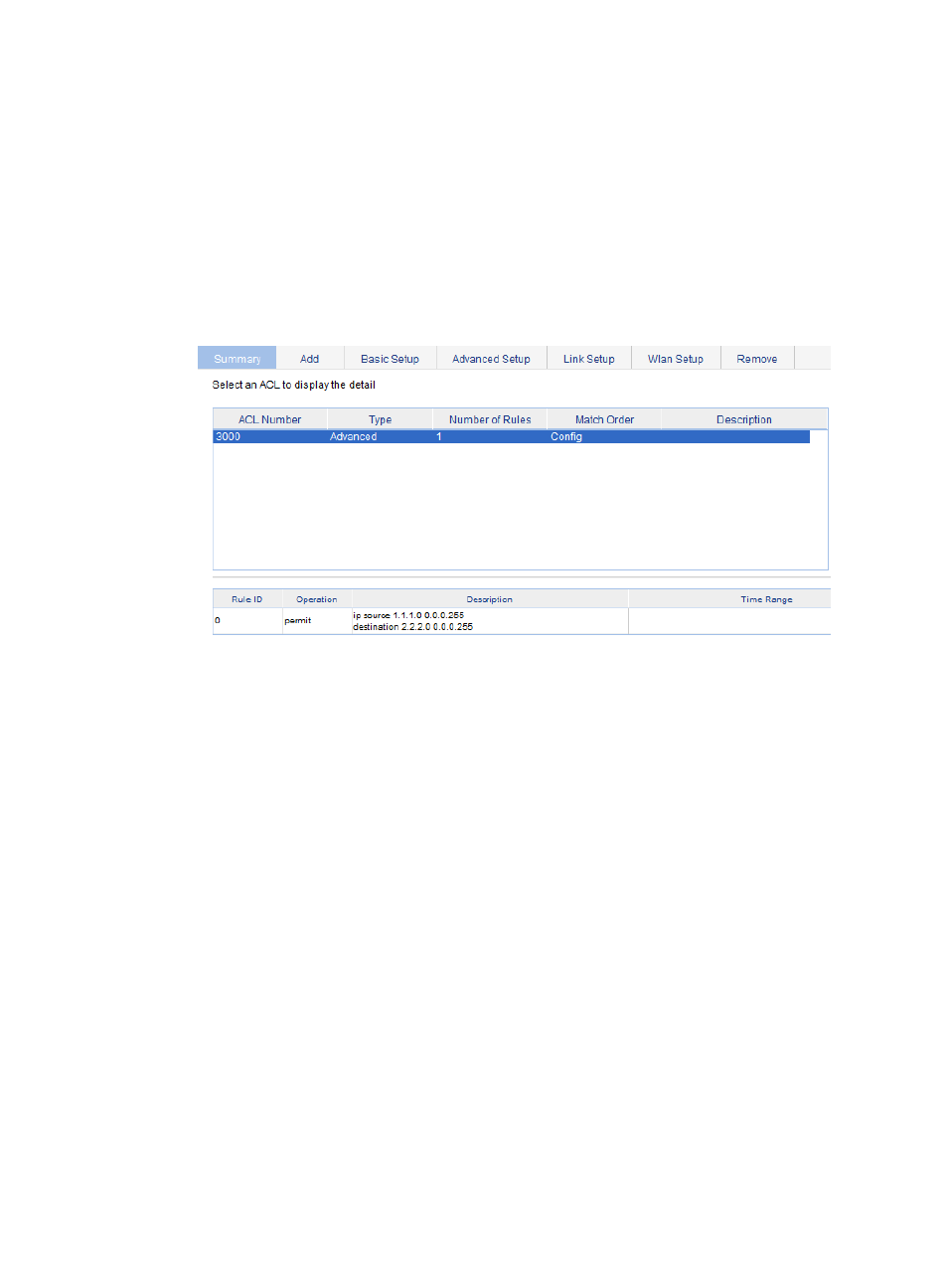
Each ACL rule matches both the outbound traffic and the returned inbound traffic. Suppose there is
a rule as shown in
. This rule matches both traffic from 1.1.1.0 to 2.2.2.0 and returned
traffic from 2.2.2.0 to 1.1.1.0.
Figure 900 An ACL referenced in an IPsec policy
•
In the outbound direction, if a permit statement is matched, IPsec considers the packet as requiring
protection and continues to process it. If a deny statement is matched or no match is found, IPsec
considers the packet as not requiring protection and delivers it to the next function module.
•
In the inbound direction, if the packet is an IPsec packet and matches a permit statement, IPsec
receives and processes the packet. If the packet is not an IPsec packet and matches a permit
statement, it is discarded.
The following uses a configuration example to show how a statement conflict causes packet drop. In this
example, only the ACL-related configurations are presented.
Device A connects the segment 1.1.2.0/24 and Device B connects the segment 3.3.3.0/24. On Device
A, apply the IPsec policy group test to the outbound interface to Device B. The IPsec policy group
contains two policies, test 1 and test 2. The ACLs referenced by the two policies each contain a rule that
matches traffic from 1.1.2.0/24 to 3.3.3.0/24. The one referenced in policy test 1 is a deny statement
and the one referenced in policy test 2 is a permit statement. Because test 1 is matched prior to test 2,
traffic from 1.1.2.0/24 to 3.3.3.0/24 will match the deny statement and sent as normal traffic. When the
traffic arrives at Device B, it will be dropped if it matches a permit statement in the ACL referenced in the
applied IPsec policy.
The configurations on Device A are shown in
,
, and
.
- H3C WX5500E Series Access Controllers H3C WX3500E Series Access Controllers H3C WX2500E Series Access Controllers H3C WX6000 Series Access Controllers H3C WX5000 Series Access Controllers H3C LSUM3WCMD0 Access Controller Module H3C LSUM1WCME0 Access Controller Module H3C LSRM1WCM2A1 Access Controller Module