Displaying and maintaining rogue detection – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 156
144
all rogue devices, only rogue APs, or only ad hoc clients. Countermeasures are not taken against wireless
bridges even if they are classified as rogues.
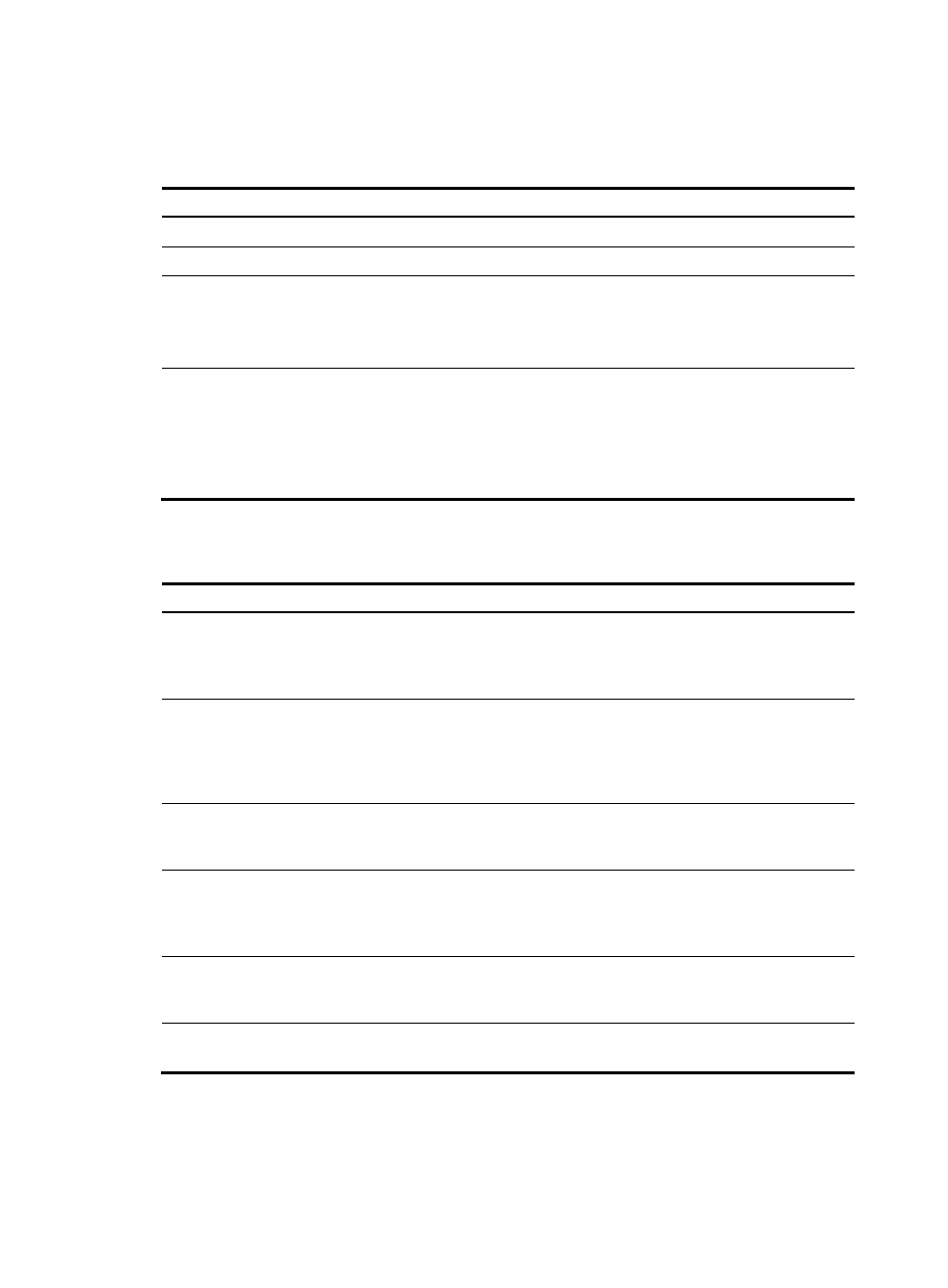
To configure the countermeasures mode:
Step Command
Remarks
1.
Enter system view.
system-view
N/A
2.
Enter WLAN IDS view.
wlan ids
N/A
3.
Configure the
countermeasures mode.
countermeasures mode { all |
{ rogue | adhoc | config } * }
Optional.
By default, the countermeasure
mode is config, or, the static attack
list.
4.
Enable the countermeasures
function.
countermeasures enable
Disabled by default.
If you want to configure the
countermeasures mode as config,
you need to use the device attack
mac-address command to
configure the static attack list first.
Displaying and maintaining rogue detection
Task Command
Remarks
Display attack list information.
display wlan ids attack-list { config |
all | ap ap-name } [ | { begin |
exclude | include }
regular-expression ]
Available in any view
Display detected entities.
display wlan ids detected { all | rogue
{ ap | client } | adhoc | ssid |
mac-address mac-address } [ | { begin
| exclude | include }
regular-expression ]
Available in any view
Display the history of attacks
detected in the WLAN system.
display wlan ids rogue-history [ |
{ begin | exclude | include }
regular-expression ]
Available in any view
Display the list of permitted
MAC addresses, the list of
permitted SSIDs, or the list of
permitted vendor OUIs..
display wlan ids permitted
{ mac-address | ssid | vendor } [ |
{ begin | exclude | include }
regular-expression ]
Available in any view
Clear the list of detected entities
in WLAN.
reset wlan ids detected { all | rogue
{ ap | client } | adhoc | ssid |
mac-address mac-address }
Available in user view
Clear all entries from the
rogue-history list.
reset wlan ids rogue-history
Available in user view