1x authentication configuration example, Network requirements, Configuration procedure – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 81
69
802.1X authentication configuration example
Network requirements
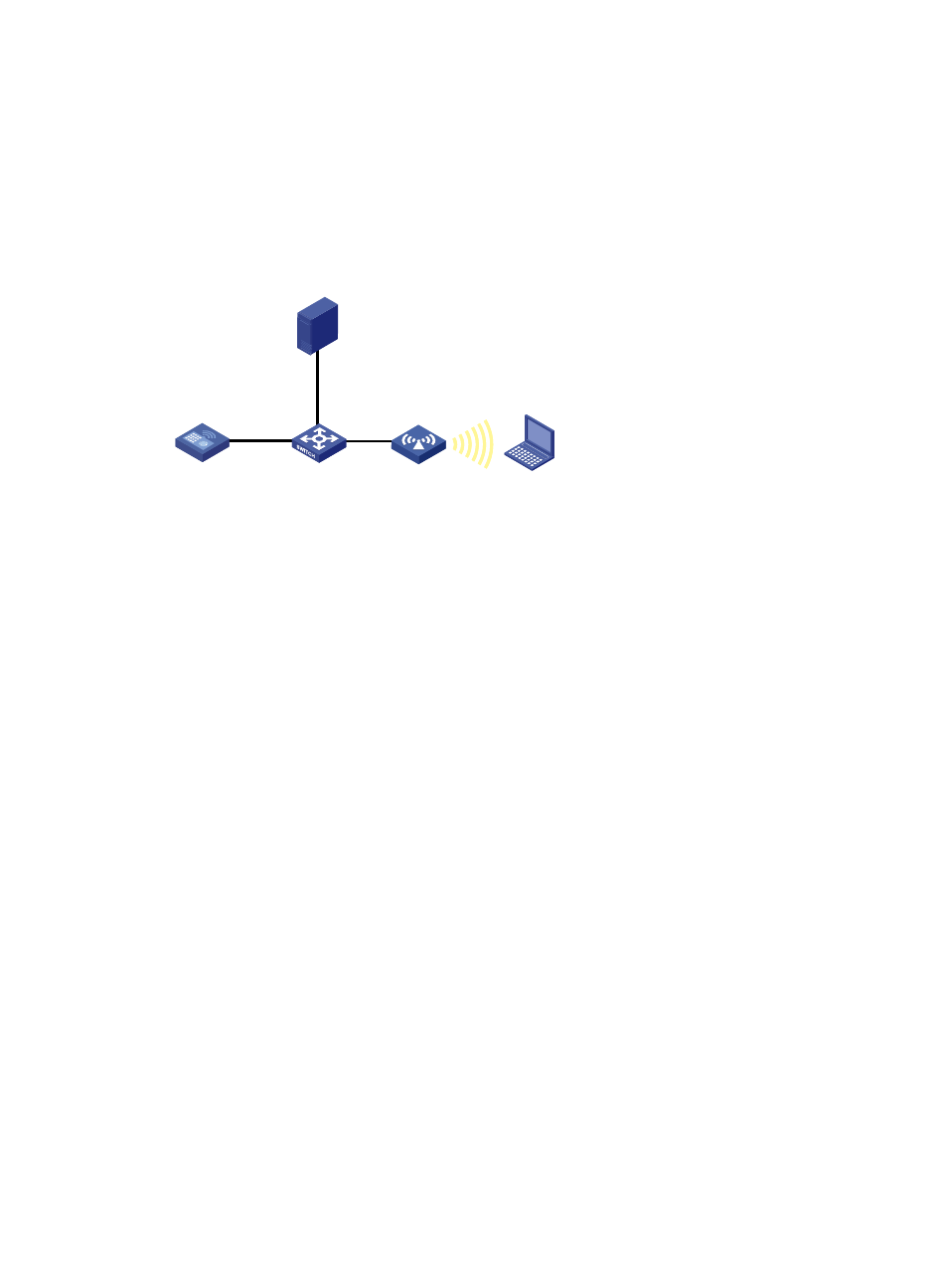
As shown in
, an AC with IP address 10.18.1.1, an AP and a RADIUS server with IP address
10.18.1.88 are connected through a Layer 2 switch. Perform 802.1X authentication on the client.
Figure 37 Network diagram
Configuration procedure
1.
Configure the AC:
# Enable port security.
<AC> system-view
[AC] port-security enable
# Configure the 802.1X authentication mode as EAP.
[AC] dot1x authentication-method eap
# Create a RADIUS scheme rad, and specify the extended RADIUS server type.
[AC] radius scheme rad
[AC-radius-rad] server-type extended
# Configure the IP addresses of the primary authentication server and accounting server as
10.18.1.88.
[AC-radius-rad] primary authentication 10.18.1.88
[AC-radius-rad] primary accounting 10.18.1.88
# Configure the shared key for RADIUS authentication/accounting packets as 12345678.
[AC-radius-rad] key authentication 12345678
[AC-radius-rad] key accounting 12345678
[AC-radius-rad] user-name-format without-domain
[AC-radius-rad] quit
# Configure AAA domain cams by referencing RADIUS scheme rad.
[AC] domain cams
[AC-isp-cams] authentication lan-access radius-scheme rad
[AC-isp-cams] authorization lan-access radius-scheme rad
[AC-isp-cams] accounting lan-access radius-scheme rad
[AC-isp-cams] quit
# Specify the mandatory domain as cams.
[AC] interface WLAN-ESS 1
10.18.1.88/24
AC
L2 switch
AP
Client
RADIUS server
10.18.1.1/24