Configuring gtk rekey based on packet, Configuring security ie, Configuring wpa security ie – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 69
57
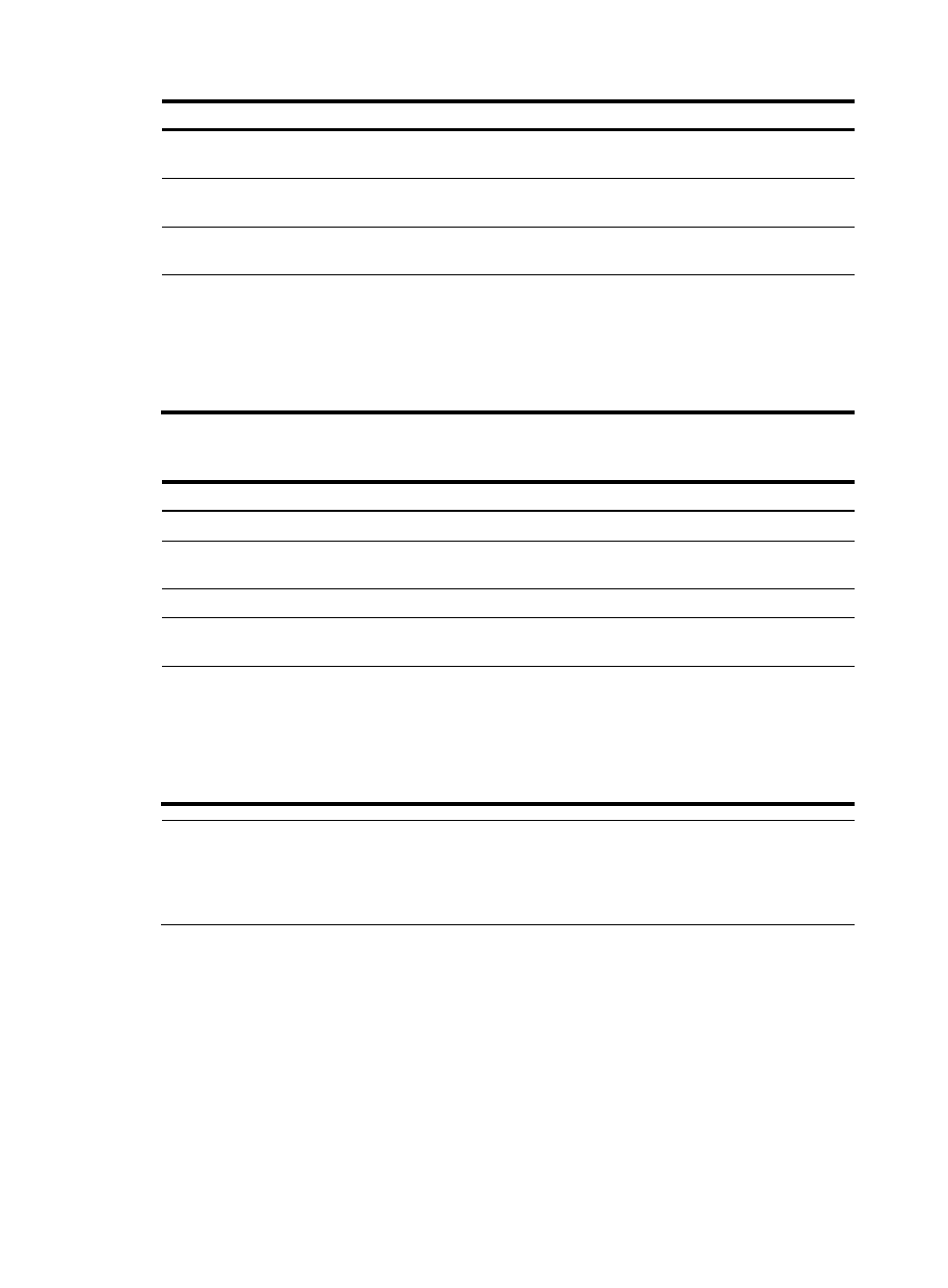
Step Command
Remarks
2.
Enter WLAN service
template view.
wlan service-template
service-template-number crypto
N/A
3.
Enable GTK rekey.
gtk-rekey enable
By default, GTK rekey is
enabled.
4.
Configure the GTK rekey
interval.
gtk-rekey method time-based [ time ]
By default, the interval is 86400
seconds.
5.
Configure the device to start
GTK rekey when a client
goes offline.
gtk-rekey client-offline enable
Optional.
Not configured by default.
The command takes effect only
when GTK rekey has been
enabled with the gtk-rekey
enable command.
Configuring GTK rekey based on packet
Step Command
Remarks
1.
Enter system view.
system-view
N/A
2.
Enter WLAN service
template view.
wlan service-template
service-template-number crypto
N/A
3.
Enable GTK rekey.
gtk-rekey enable
By default, GTK rekey is enabled.
4.
Configure GTK rekey based
on packet.
gtk-rekey method packet-based
[ packet ]
The default packet number is
10000000.
5.
Configure the device to start
GTK rekey when a client
goes offline.
gtk-rekey client-offline enable
Optional.
Not configured by default.
This command takes effect only
when GTK rekey has been
enabled with the gtk-rekey
enable command.
NOTE:
•
By default, time-based GTK rekey is adopted, and the rekey interval is 86400 seconds.
•
Configuring a new GTK rekey method overwrites the previous one. For example, if time-based GTK
rekey is configured after packet-based GTK rekey is configured, time-based GTK rekey takes effect.
Configuring security IE
Configuring WPA security IE
WPA ensures greater protection than WEP. WPA operates in either WPA-PSK (or Personal) mode or
WPA-802.1X (or Enterprise) mode. In Personal mode, a pre-shared key or pass-phrase is used for
authentication. In Enterprise mode, 802.1X and RADIUS servers and the Extensible Authentication
Protocol (EAP) are used for authentication.
To configure the WPA security IE: