Configuring ids attack detection, Displaying and maintaining ids attack detection, Wlan ids configuration example – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 157: Network requirements, Displaying and maintaining ids, Attack detection
145
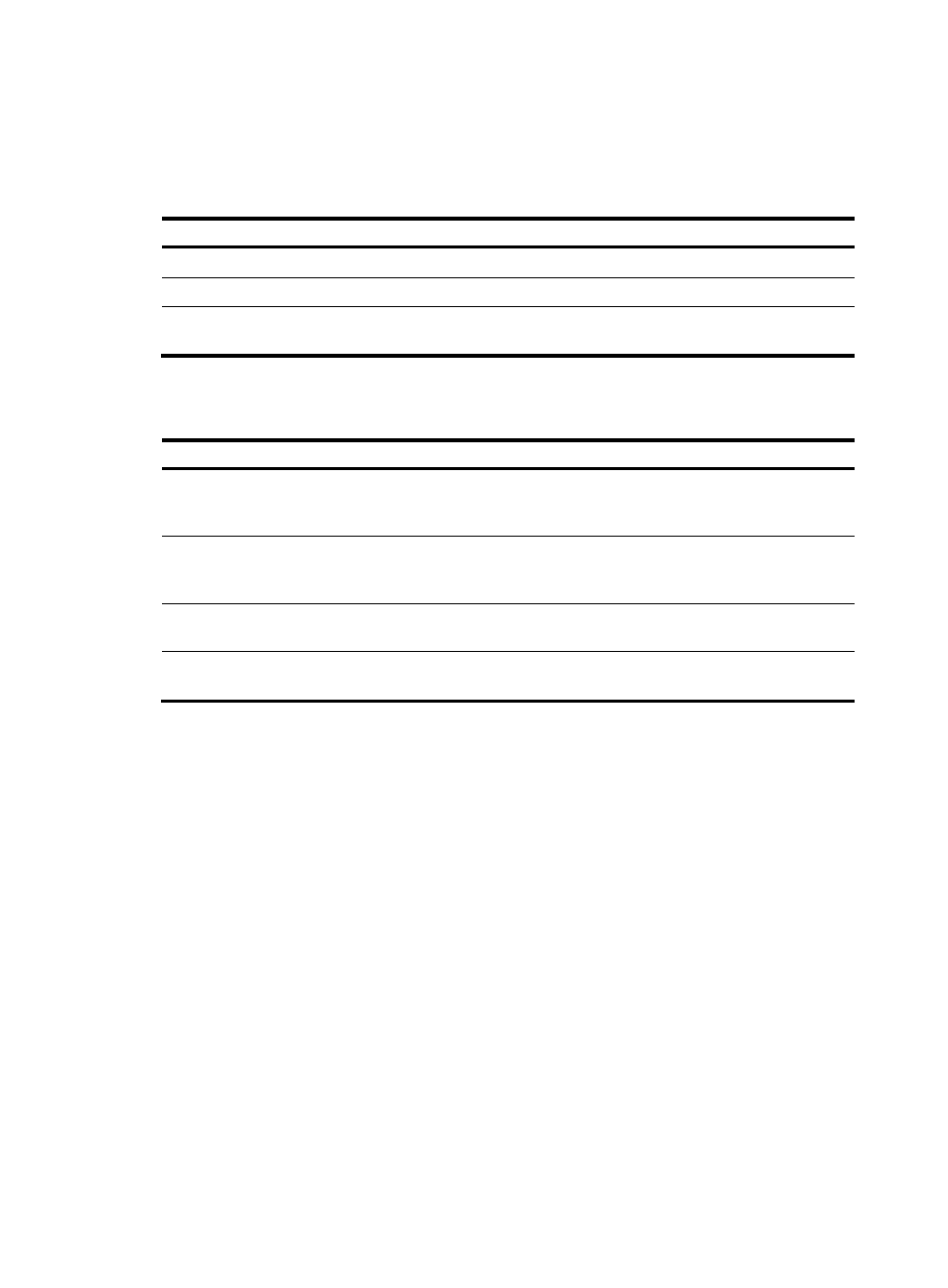
Configuring IDS attack detection
Configuring IDS attack detection
Step Command
Remarks
1.
Enter system view.
system-view
N/A
2.
Enter IDS view.
wlan ids
N/A
3.
Enable IDS attack detection.
attack-detection enable { all | flood
| weak-iv | spoof }
Disabled by default.
Displaying and maintaining IDS attack detection
Task Command
Remarks
Display all the attacks detected
by WLAN IDS IPS.
display wlan ids history [ | { begin |
exclude | include }
regular-expression ]
Available in any view
Display the count of attacks
detected by WLAN IDS IPS.
display wlan ids statistics [ | { begin |
exclude | include }
regular-expression ]
Available in any view
Clear the history of attacks
detected by the WLAN system. reset wlan ids history
Available in user view
Clear the statistics of attacks
detected in the WLAN system.
reset wlan ids statistics
Available in user view
WLAN IDS configuration example
Network requirements
As shown in
, a monitor AP (with serial ID 210235A29G007C000020) and AP1 (serial ID
210235A29G007C000021) are connected to an AC through a Layer 2 switch.
•
AP1 operates in normal mode, and only provides WLAN services.
•
AP2 operates in monitor mode, and detects rogue devices.
•
Client 1 (MAC address 000f-e215-1515), Client 2 (MAC address 000f-e215-1530) and Client 3
(MAC address 000f-e213-1235) are connected to AP1.
•
Client 4 (MAC address 000f-e220-405e) are considered as rogues.