Configuring user isolation, Introduction to vlan-based user isolation – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 39
27
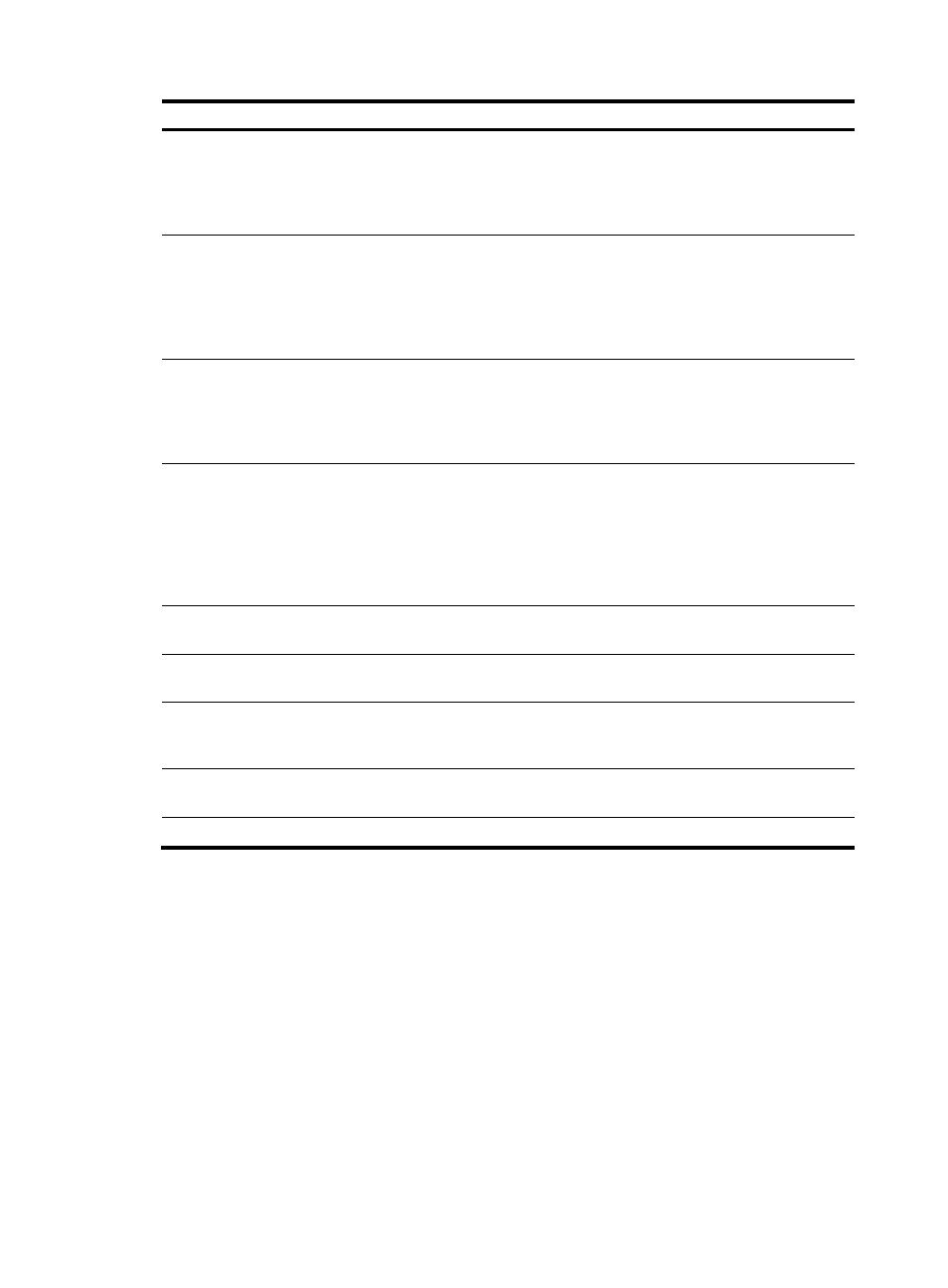
Task Command
Remarks
Display service template statistics.
display wlan statistics
service-template
service-template-number [ | { begin
| exclude | include }
regular-expression ]
Available in any view
Display the connection history for
all APs bound to a service
template.
display wlan statistics
service-template
service-template-number
connect-history [ | { begin |
exclude | include }
regular-expression ]
Available in any view
Display WLAN statistics.
display wlan statistics { client { all |
mac-address mac-address } |
radio [ ap-name ] } [ | { begin |
exclude | include }
regular-expression ]
Available in any view.
Display WLAN client information.
display wlan client { ap ap-name
[ radio radio-number ] |
mac-address mac-address |
service-template
service-template-number }
[ verbose ] [ | { begin | exclude |
include } regular-expression ]
Available in any view
Reset AP connections.
reset wlan ap { all | name
ap-name }
Available in user view
Clear AP reboot logs.
reset wlan ap reboot-log { all |
name ap-name }
Available in user view
Clear AP or client statistics.
reset wlan statistics { client { all |
mac-address mac-address } |
radio [ ap-name ] }
Available in user view
Cut off WLAN clients.
reset wlan client { all |
mac-address mac-address }
Available in user view
RFPing a wireless client.
wlan link-test mac-address
Available in user view
Configuring user isolation
Introduction to VLAN-based user isolation
Without VLAN-based user isolation, devices in the same VLAN can access each other at Layer-2, which
could result in security problems. VLAN-based user isolation is designed to solve this problem. When an
AC configured with user isolation receives unicast packets (broadcast packets and multicast packets in a
VLAN are not isolated) from a wireless client to another wireless client or wired PC in the same VLAN, or
from a wired PC to a wireless client in the same VLAN, the AC determines whether to isolate the two
devices according to the configured list of permitted MAC addresses.
To avoid user isolation from affecting communications between hosts and the gateway, you can add the
MAC address of the gateway to the list of permitted MAC addresses.