Chapter 52 802.1x configuration, 1 introduction to 802.1x, 1 the authentication structure of 802.1x – PLANET XGS3-24042 User Manual
Page 515: Chapter 52 802.1x configuration -1, Ntroduction to, 1 the authentication structure of 802.1x -1
52-1
Chapter 52 802.1x Configuration
52.1 Introduction to 802.1x
The 802.1x protocol originates from 802.11 protocol, the wireless LAN protocol of IEEE, which is designed to
provide a solution to doing authentication when users access a wireless LAN. The LAN defined in IEEE 802
LAN protocol does not provide access authentication, which means as long as the users can access a LAN
controlling device (such as a LAN Switch), they will be able to get all the devices or resources in the LAN.
There was no looming danger in the environment of LAN in those primary enterprise networks.
However, along with the boom of applications like mobile office and service operating networks, the service
providers should control and configure the access from user. The prevailing application of WLAN and LAN
access in telecommunication networks, in particular, make it necessary to control ports in order to implement
the user-level access control. And as a result, IEEE LAN/WAN committee defined a standard, which is 802.1x,
to do Port-Based Network Access Control. This standard has been widely used in wireless LAN and ethernet.
“Port-Based Network Access Control” means to authenticate and control the user devices on the level of ports
of LAN access devices. Only when the user devices connected to the ports pass the authentication, can they
access the resources in the LAN, otherwise, the resources in the LAN won’t be available.
52.1.1 The Authentication Structure of 802.1x
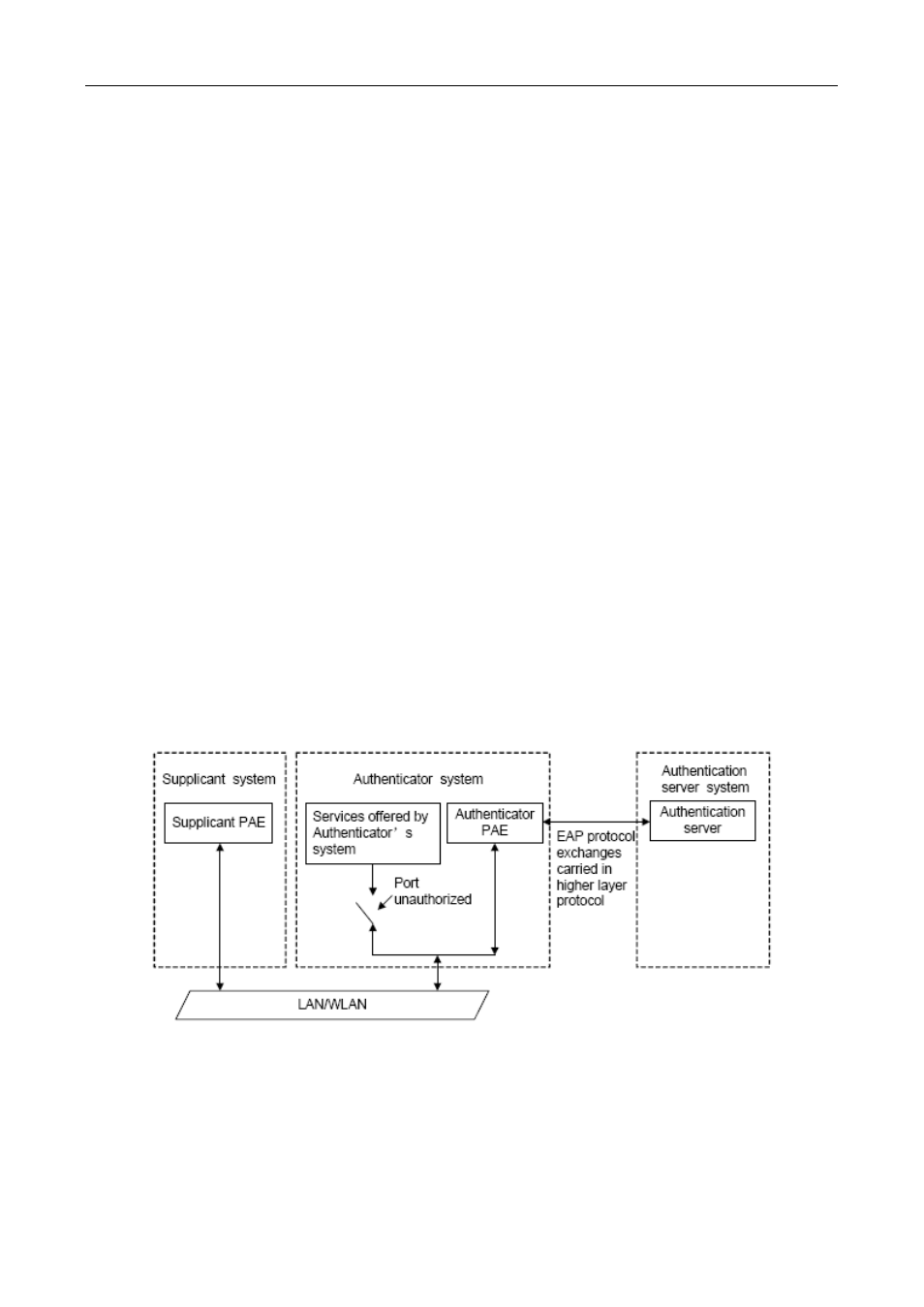
The system using 802.1x has a typical Client/Server structure, which contains three entities (as illustrated in
the next figure): Supplicant system, Authenticator system, and Authentication server system.
Figure 52-1 The Authentication Structure of 802.1x
The supplicant system is an entity on one end of the LAN segment, should be authenticated by the
access controlling unit on the other end of the link. A Supplicant system usually is a user terminal
device. Users start 802.1x authentication by starting supplicant system software. A supplicant