Relationship between ike and ipsec, Protocols and standards, Configuration prerequisites – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 846: Recommended configuration procedure
825
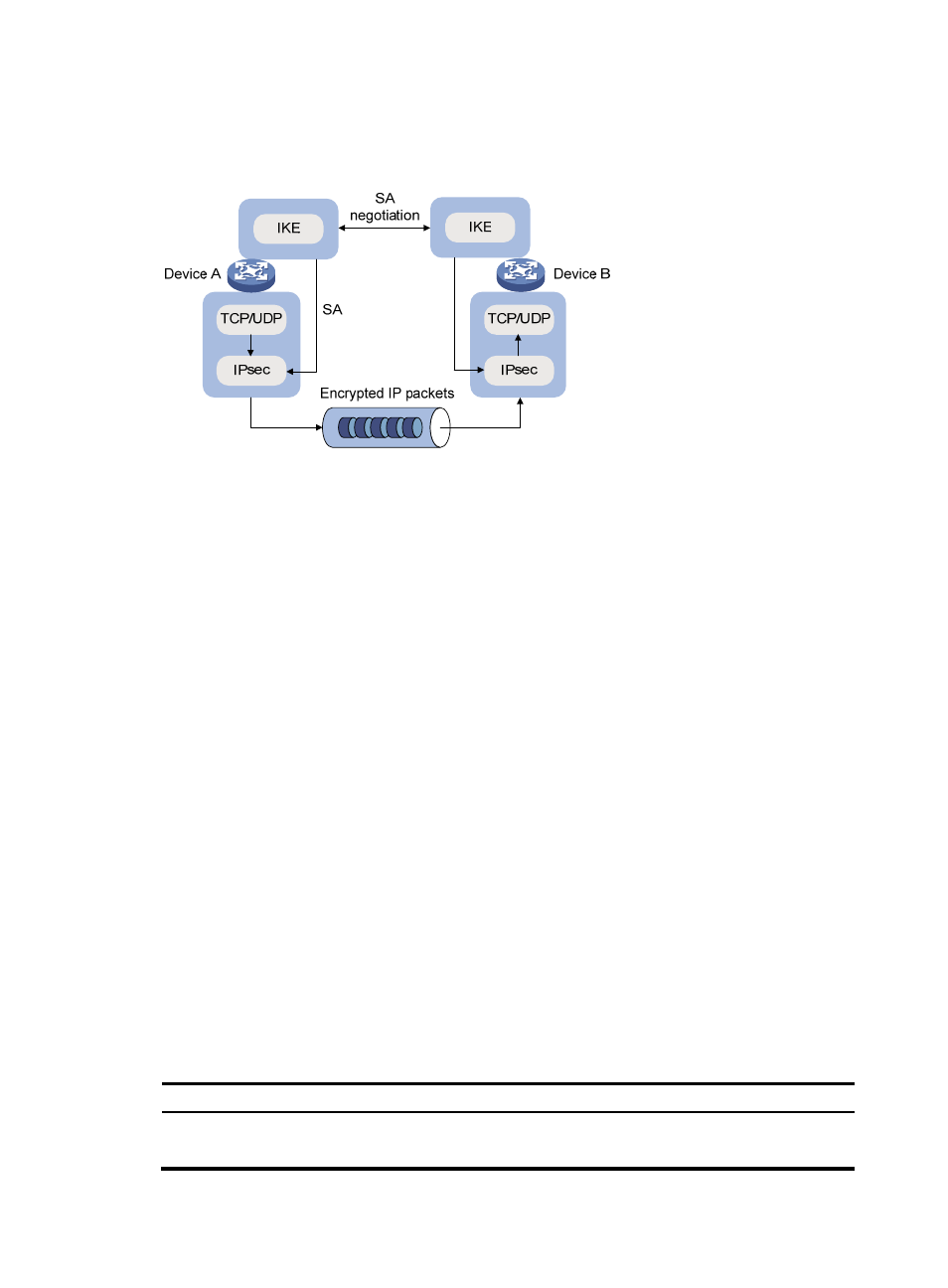
Relationship between IKE and IPsec
Figure 879 Relationship between IKE and IPsec
illustrates the relationship between IKE and IPsec:
•
IKE is an application layer protocol using UDP and functions as the signaling protocol of IPsec.
•
IKE negotiates SAs for IPsec and delivers negotiated parameters and generated keys to IPsec.
•
IPsec uses the SAs set up through IKE negotiation for encryption and authentication of IP packets.
Protocols and standards
•
RFC 2408, Internet Security Association and Key Management Protocol (ISAKMP)
•
RFC 2409, The Internet Key Exchange (IKE)
•
RFC 2412, The OAKLEY Key Determination Protocol
Configuration prerequisites
Before you configure IKE, verify the following parameters:
•
The strength of the algorithms for IKE negotiation (the security protection level), including the
identity authentication method, encryption algorithm, authentication algorithm, and DH group.
Different algorithms provide different levels of protection. A stronger algorithm means more resistant
to decryption of protected data but requires more resources. Generally, the longer the key, the
stronger the algorithm.
•
The pre-shared key or the PKI domain to which the certificate belongs. For more information about
PKI configuration, see "
."
Recommended configuration procedure
Step Remarks
Optional.
Configure the IKE local name and NAT keepalive interval.