Configuring ike dpd – H3C Technologies H3C WX3000E Series Wireless Switches User Manual
Page 850
829
Item
Description
Authentication
Algorithm
Select the authentication algorithm to be used by the IKE proposal. Options include:
•
SHA1—Uses HMAC-SHA1.
•
MD5—Uses HMAC-MD5.
Encryption
Algorithm
Select the encryption algorithm to be used by the IKE proposal. Options include:
•
DES-CBC—Uses the DES algorithm in CBC mode and 56-bit keys for encryption.
•
3DES-CBC—Uses the 3DES algorithm in CBC mode and 168-bit keys for encryption.
•
AES-128—Uses the AES algorithm in CBC mode and 128-bit keys for encryption.
•
AES-192—Uses the AES algorithm in CBC mode and 192-bit keys for encryption.
•
AES-256—Uses the AES algorithm in CBC mode and 256-bit keys for encryption.
DH Group
Select the DH group to be used in key negotiation phase 1. Options include:
•
Group1—Uses the 768-bit Diffie-Hellman group.
•
Group2—Uses the 1024-bit Diffie-Hellman group.
•
Group5—Uses the 1536-bit Diffie-Hellman group.
•
Group14—Uses the 2048-bit Diffie-Hellman group.
SA Lifetime
Enter the ISAKMP SA lifetime of the IKE proposal.
Before an SA expires, IKE negotiates a new SA. As soon as the new SA is set up, it takes
effect immediately and the old one will be cleared automatically when it expires.
IMPORTANT:
If the SA lifetime expires, the system automatically updates the ISAKMP SA. DH calculation
in IKE negotiation takes time, especially on low-end devices. Set the lifetime greater than 10
minutes to prevent the SA update from influencing normal communication.
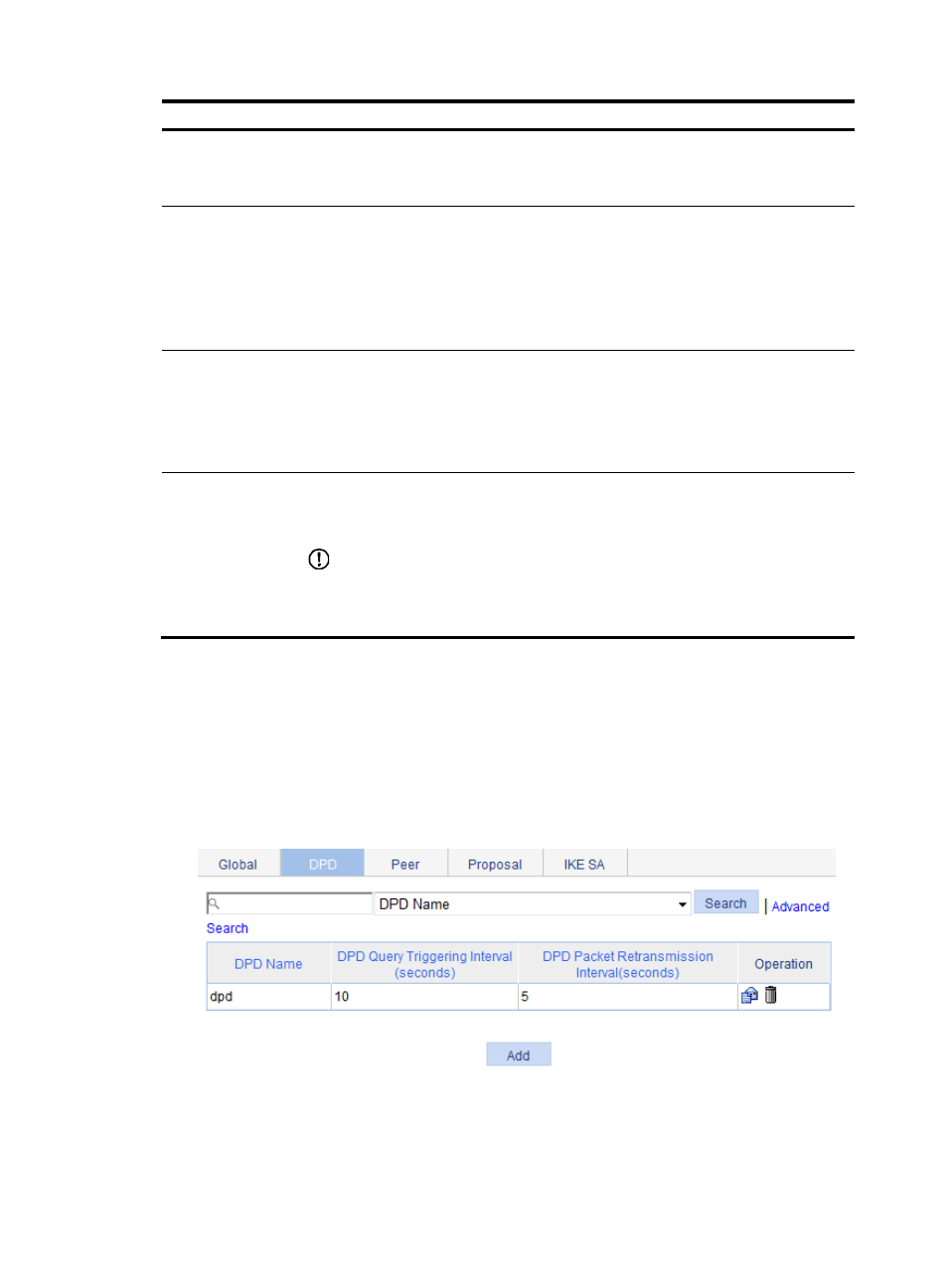
Configuring IKE DPD
1.
From the navigation tree, select VPN > IKE.
2.
Click the DPD tab.
The DPD detector list page appears.
Figure 883 DPD detector list
3.
Click Add.
The Add IKE DPD page appears.